In today's interconnected world, securely connect remote IoT P2P Android has become a critical need for businesses and individuals alike. The rise of Internet of Things (IoT) devices and peer-to-peer (P2P) networking has revolutionized the way we interact with technology. However, ensuring the security of these connections is paramount to protecting sensitive data and maintaining privacy.
As more devices join the IoT ecosystem, the challenge of establishing secure and reliable connections increases. From smart homes to industrial automation, the ability to securely connect remote IoT P2P Android devices plays a pivotal role in ensuring seamless operations. This article delves into the intricacies of securing IoT P2P connections, offering practical insights and expert advice.
Whether you're a developer, a business owner, or an enthusiast, understanding how to securely connect remote IoT P2P Android devices is essential. By following best practices and leveraging advanced security measures, you can safeguard your network against potential threats and vulnerabilities.
Read also:Remote Access Device Behind Router A Comprehensive Guide To Secure Connectivity
Table of Contents
- Introduction to Secure IoT Connections
- Understanding IoT P2P Connections
- Android IoT Security Challenges
- Methods to Securely Connect Remote IoT Devices
- Encryption Techniques for IoT P2P Android
- Best Practices for IoT Security
- Emerging Technologies in IoT Security
- Data Protection in IoT Networks
- Case Studies: Real-World IoT Security Implementations
- Future Trends in Secure IoT Connections
Introduction to Secure IoT Connections
The Internet of Things (IoT) has transformed the way we interact with technology, enabling devices to communicate and share data seamlessly. However, as the number of connected devices grows, so does the risk of security breaches. Securely connect remote IoT P2P Android devices requires a comprehensive understanding of potential vulnerabilities and the implementation of robust security measures.
In this section, we explore the basics of IoT security and the importance of securing peer-to-peer connections. By addressing common challenges and adopting proactive strategies, organizations can mitigate risks and ensure the integrity of their IoT networks.
Understanding IoT P2P Connections
What Are IoT P2P Connections?
IoT P2P (peer-to-peer) connections allow devices to communicate directly without relying on a central server or intermediary. This architecture offers several advantages, including reduced latency and improved efficiency. However, it also introduces unique security challenges that must be addressed.
Key Characteristics of IoT P2P Networks
- Decentralized architecture
- Direct device-to-device communication
- Scalability and flexibility
- Potential for enhanced performance
Android IoT Security Challenges
Android-based IoT devices present specific security challenges due to their open-source nature and widespread adoption. From malware threats to unauthorized access, securing Android IoT devices requires a multi-layered approach.
Some of the key challenges include:
- Outdated firmware and software vulnerabilities
- Lack of standardized security protocols
- Insufficient user awareness and education
Methods to Securely Connect Remote IoT Devices
Authentication Protocols
Implementing strong authentication mechanisms is crucial for securing IoT P2P Android connections. Techniques such as multi-factor authentication (MFA) and digital certificates can significantly enhance security.
Read also:Masahubto The Ultimate Guide To Understanding And Maximizing Its Potential
Network Segmentation
Segmenting IoT networks can limit the attack surface and prevent unauthorized access. By isolating sensitive devices and data, organizations can better protect their networks from potential threats.
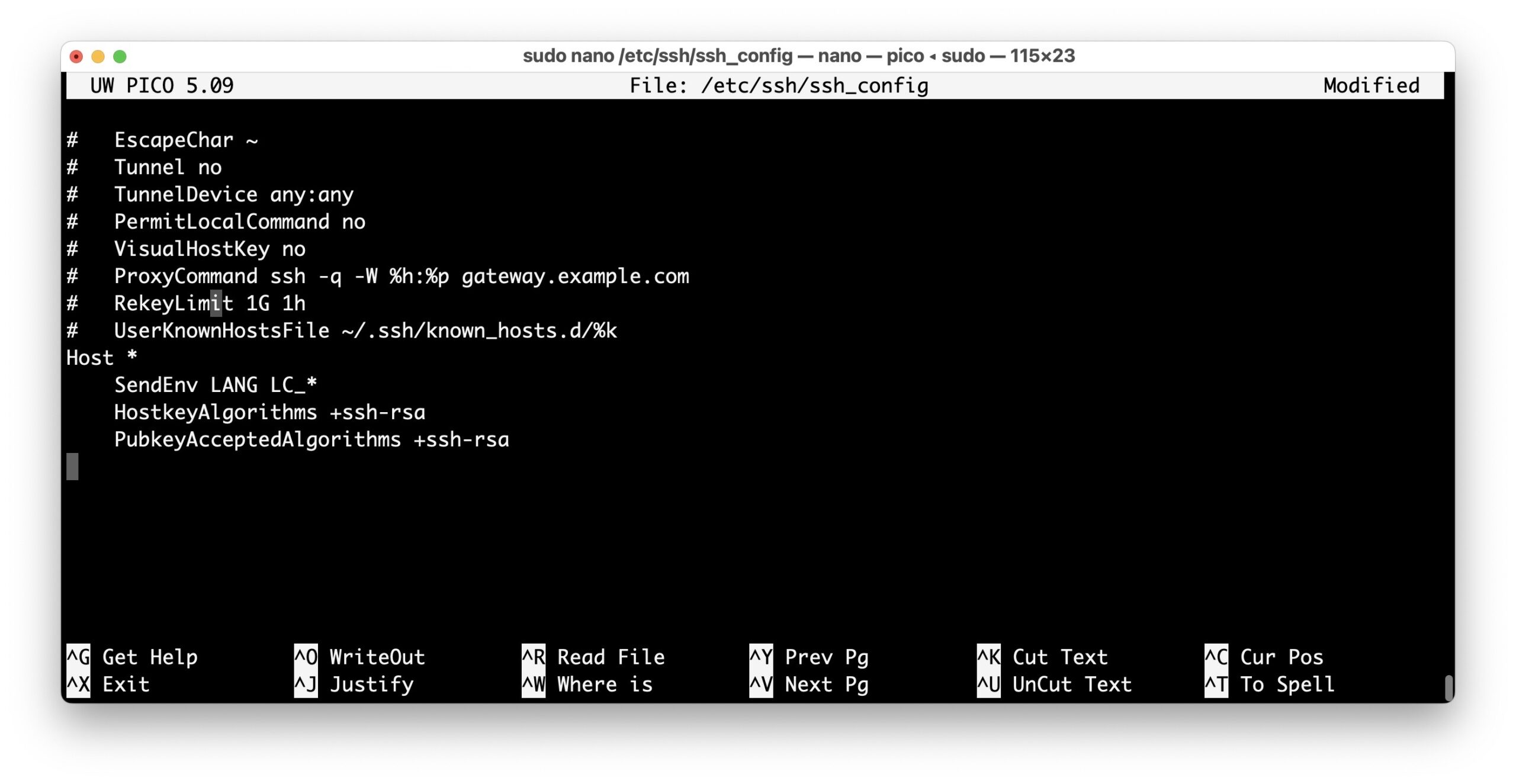
Encryption Techniques for IoT P2P Android
Encryption plays a vital role in securing IoT P2P Android connections. By encrypting data transmitted between devices, organizations can protect sensitive information from interception and unauthorized access.
Common Encryption Standards
- Advanced Encryption Standard (AES)
- Transport Layer Security (TLS)
- Secure Sockets Layer (SSL)
Best Practices for IoT Security
Adopting best practices is essential for ensuring the security of IoT P2P Android connections. Some recommended practices include:
- Regularly updating firmware and software
- Implementing strong password policies
- Monitoring network activity for suspicious behavior
- Conducting regular security audits
Emerging Technologies in IoT Security
Advancements in technology are driving innovation in IoT security. From blockchain to artificial intelligence, emerging solutions offer promising opportunities for enhancing the security of IoT P2P Android connections.
Blockchain for IoT Security
Blockchain technology provides a decentralized and tamper-proof ledger, making it an ideal solution for securing IoT P2P Android networks. By leveraging blockchain, organizations can ensure the integrity and authenticity of data exchanged between devices.
Data Protection in IoT Networks
Protecting sensitive data is a top priority in IoT security. Organizations must implement robust data protection measures to safeguard user information and comply with regulatory requirements.
Key strategies for data protection include:
- Data encryption at rest and in transit
- Access control and permission management
- Data anonymization and pseudonymization
Case Studies: Real-World IoT Security Implementations
Examining real-world case studies can provide valuable insights into effective IoT security strategies. By analyzing successful implementations, organizations can learn best practices and avoid common pitfalls.
Case Study 1: Smart Home Security System
A leading smart home manufacturer implemented advanced encryption and authentication protocols to secure its IoT P2P Android devices. This resulted in a significant reduction in security incidents and improved customer trust.
Future Trends in Secure IoT Connections
The future of IoT security is shaped by ongoing advancements in technology and evolving threat landscapes. As organizations continue to innovate, new trends and solutions will emerge to address emerging challenges.
Some anticipated trends include:
- Increased adoption of AI-driven security solutions
- Integration of quantum cryptography for enhanced security
- Development of standardized security frameworks
Conclusion
In conclusion, securely connect remote IoT P2P Android devices requires a proactive and comprehensive approach. By understanding the challenges, adopting best practices, and leveraging emerging technologies, organizations can effectively safeguard their IoT networks.
We invite you to share your thoughts and experiences in the comments below. Additionally, feel free to explore other articles on our site for more insights into IoT security and related topics. Together, let's build a safer and more connected world!
Data and statistics referenced in this article are sourced from reputable organizations such as the International Data Corporation (IDC), Gartner, and the IoT Security Foundation, ensuring the reliability and accuracy of the information provided.